Introduction
In an era where digital threats are increasingly prevalent, educational institutions are tasked with the critical responsibility of safeguarding sensitive information. Effective information security planning is not merely a necessity; it is essential for protecting students, staff, and the integrity of the institution. This article explores four best practices that schools can implement to strengthen their information security frameworks, addressing the vital question: how can schools navigate the complexities of cybersecurity while ensuring a safe learning environment?
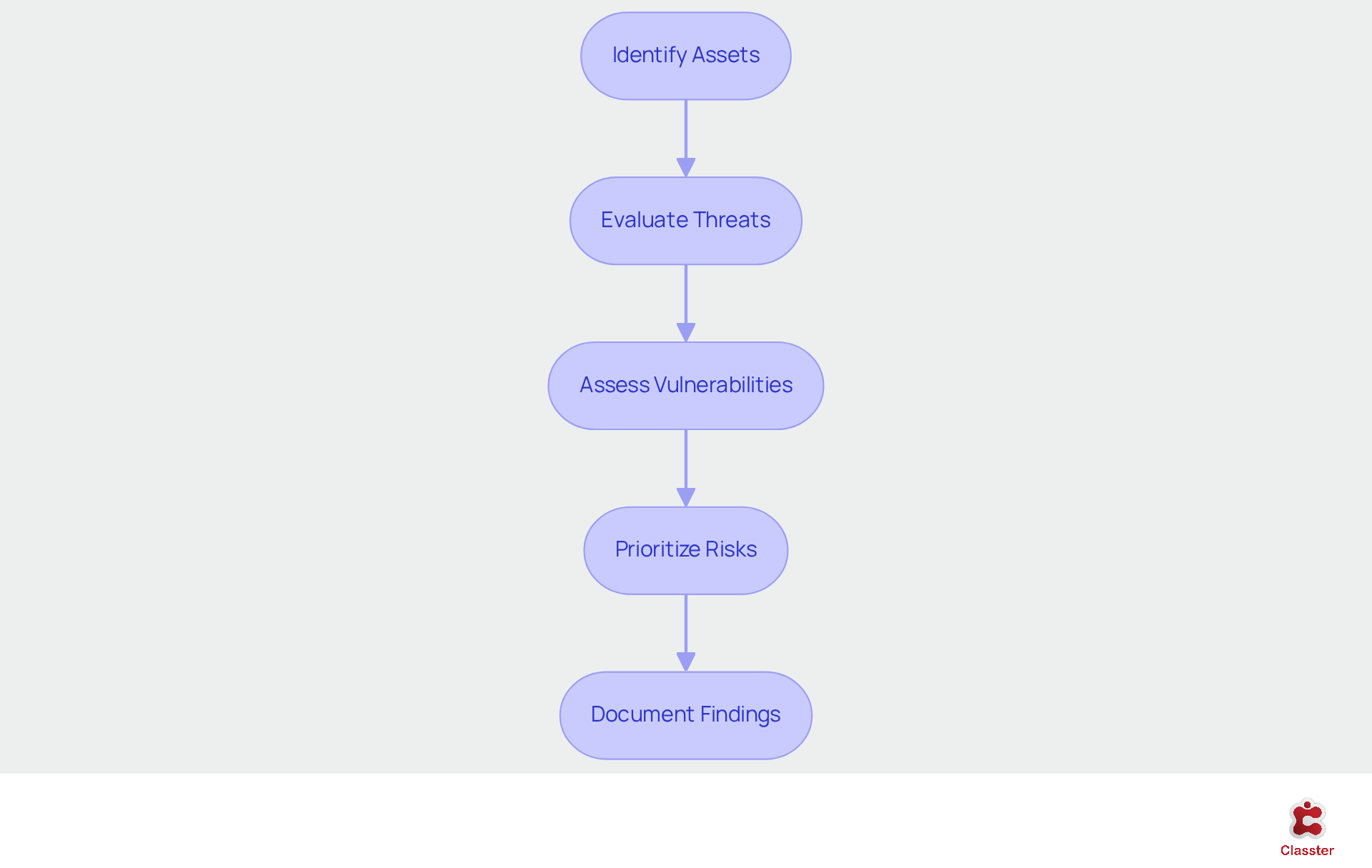
Conduct Comprehensive Risk Assessments
To effectively safeguard sensitive information, educational institutions must conduct comprehensive risk assessments regularly. This process involves identifying potential threats, evaluating vulnerabilities, and assessing the impact of various risks on the institution. Schools should assemble a risk assessment team that includes IT staff, administrators, and educators to ensure a holistic approach.
- Identify Assets: Begin by cataloging all digital assets, including student records, financial data, and communication systems. Understanding what needs protection is the first step in risk management.
- Evaluate Threats: Analyze potential threats such as cyber-attacks, data breaches, and natural disasters. Utilize resources such as the NCSC’s guidelines on cyber protection in educational institutions to inform this evaluation, ensuring alignment with Classter’s safety practices.
- Assess Vulnerabilities: Identify weaknesses in current protective measures, such as outdated software or insufficient access controls. Regularly updating systems and employing tools like vulnerability scanners can assist in this regard. Classter’s all-in-one school management system enhances operational efficiency, facilitating the management of courses, communication, and billing processes while ensuring robust data protection.
- Prioritize Risks: After identifying threats and vulnerabilities, prioritize them based on their potential impact and likelihood. This prioritization will guide resource allocation and investment in safety measures.
- Document Findings: Maintain comprehensive records of the assessment process and results to inform future protection strategies and compliance requirements. By conducting these evaluations at least once a year, schools can adapt to evolving risks and ensure that their protective measures remain effective, demonstrating Classter’s commitment to safeguarding educational institutions.
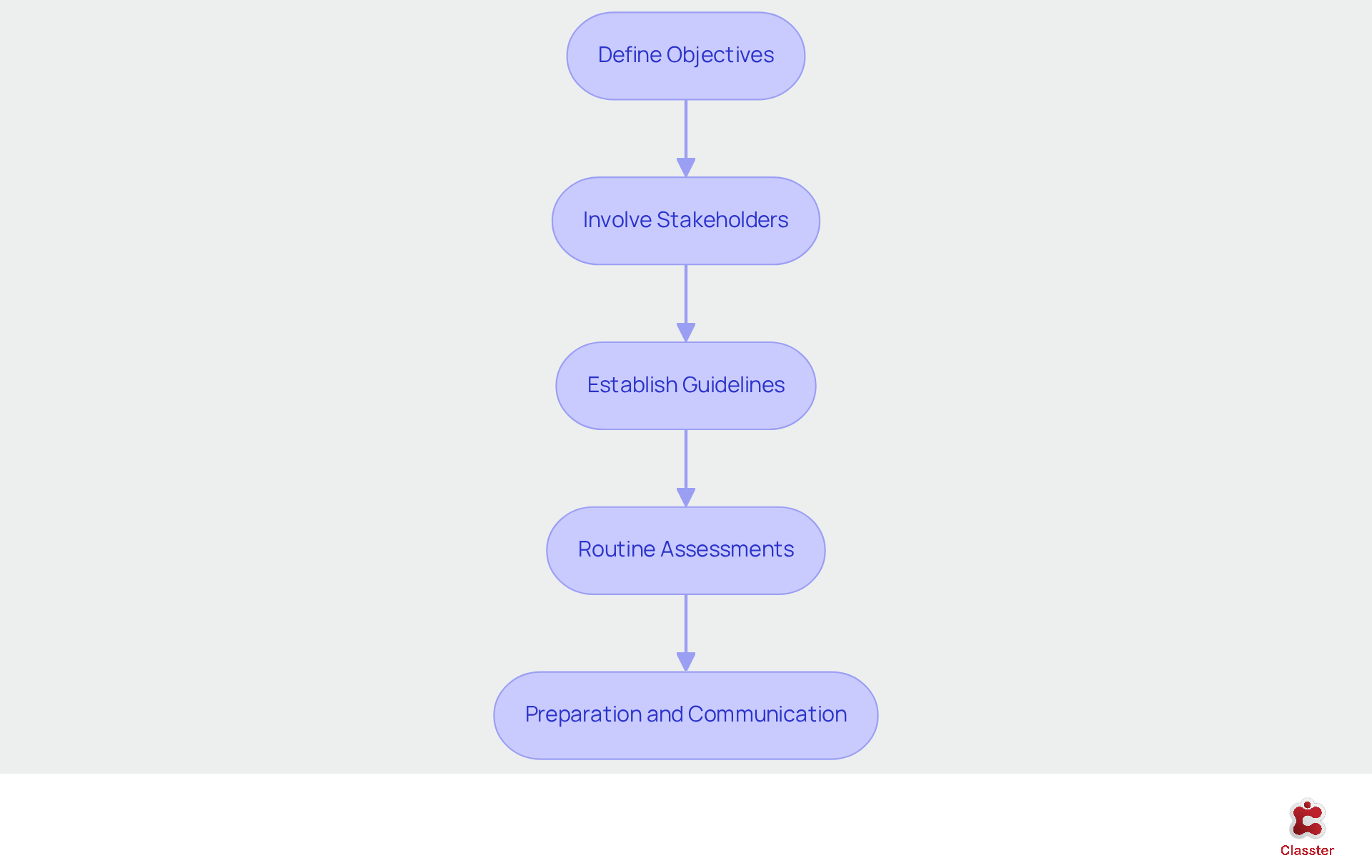
Develop Tailored Information Security Policies
Developing customized information protection guidelines is essential for fostering a secure environment in educational institutions. These regulations must be comprehensive, addressing various aspects of data protection and user responsibilities.
Define Objectives: Clearly articulate the goals of the information security planning framework, emphasizing the protection of student data and compliance with regulations such as FERPA and GDPR.
Involve Stakeholders: Engage key stakeholders-including IT staff, educators, and administrators-in the development process to ensure that the guidelines are practical, relevant, and reflective of the institution’s unique needs.
Establish Guidelines: Develop specific guidelines for data access, sharing, and storage. This should include protocols for handling sensitive information and responding to potential data breaches, ensuring that all staff are aware of their responsibilities.
Routine Assessments: Establish a timetable for regular evaluations of the guidelines to maintain their relevance and effectiveness in addressing emerging threats and technological advancements.
Preparation and Communication: Provide thorough instruction for all personnel and learners on the guidelines, ensuring they understand their responsibilities in upholding information protection. Utilizing platforms like Classter can facilitate the dissemination of information and effectively track compliance.
By adopting customized information security planning, educational institutions can create a structured approach to data protection, significantly enhancing their overall security posture and fostering trust among stakeholders.
Implement Ongoing Training and Awareness Programs
Continuous education and awareness initiatives are essential for sustaining a robust cybersecurity posture in schools. These initiatives should prioritize educating both staff and students about prevalent cybersecurity threats and effective best practices.
- Regular Workshops: Frequent workshops and sessions should be arranged to cover essential topics such as phishing awareness, password management, and safe internet practices. Utilizing resources from reputable organizations can help create effective educational materials. Notably, the percentage of educators receiving cybersecurity education increased from 61% to 72% between the academic years 2023-2024 and 2024-2025, underscoring the growing recognition of the necessity for such instruction.
- Interactive Learning: Integrating interactive components, including quizzes and simulations, can engage participants and reinforce their understanding. This approach enhances the retention of critical information among both staff and students.
- Tailored Content: Instructional materials should be adapted to meet the specific needs and risks of the school environment. For example, it is important to emphasize the unique challenges associated with remote learning scenarios.
- Feedback Mechanisms: Establishing feedback systems is crucial for assessing the effectiveness of educational programs and implementing necessary adjustments. Surveys and assessments can identify areas needing improvement. Nearly two-thirds of safety leaders agree that traditional educational models are inadequate in ensuring cyber resilience, highlighting the importance of ongoing enhancement based on feedback.
- Promote a Safety Culture: Fostering a culture of safety involves recognizing and rewarding individuals who demonstrate exemplary protective practices. This strategy can inspire others to prioritize cybersecurity in their daily routines. Amanda Swann, Ofqual’s Executive Director, remarked that ‘Cyber attacks can have a devastating impact on students’ academic work,’ emphasizing the critical need for continuous education.
By committing to continuous training, schools can empower their communities to effectively recognize and address threats, ultimately enhancing overall safety and resilience.

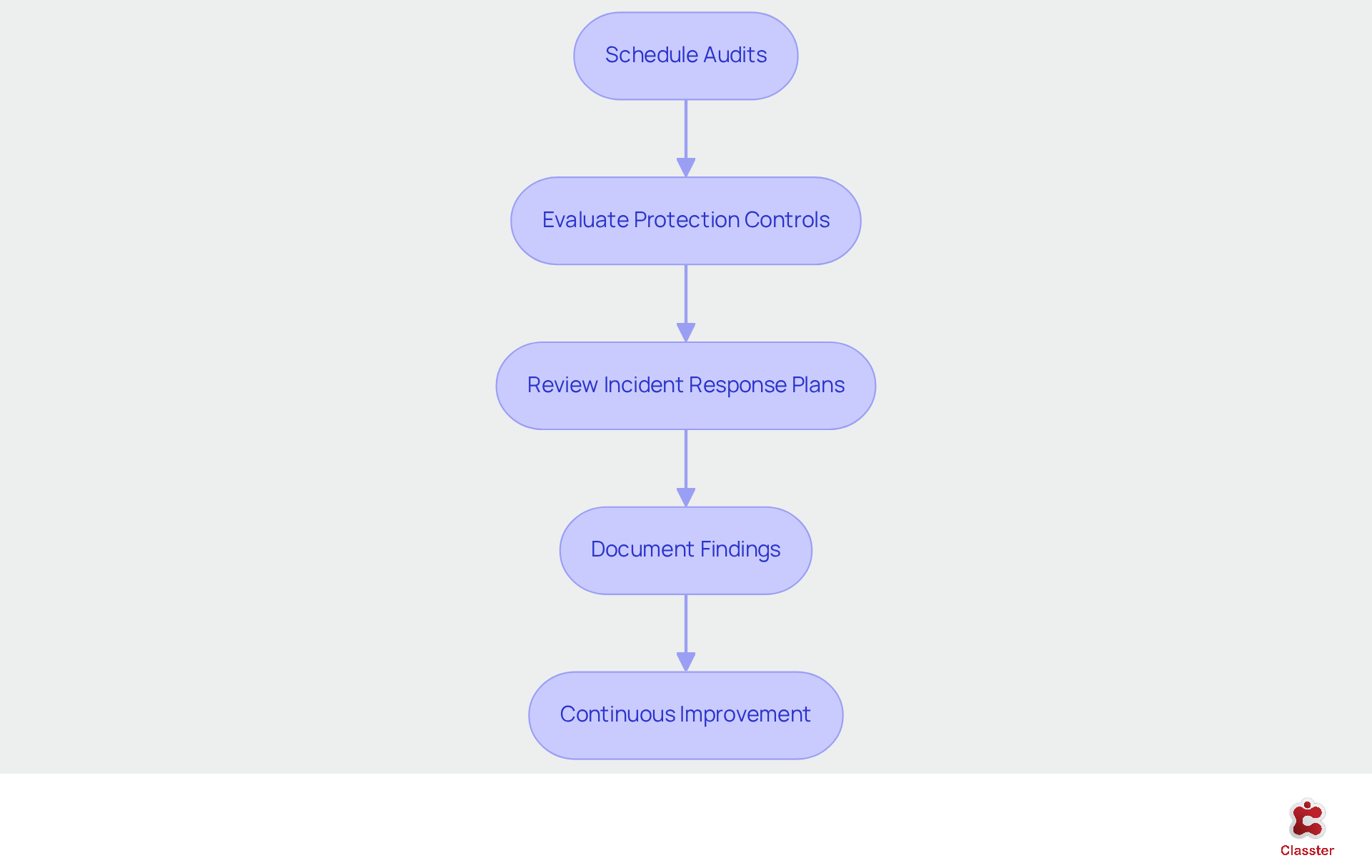
Conduct Regular Security Audits and Updates
Regular safety assessments and updates are essential for effective information security planning to establish a robust information protection framework in educational institutions. These audits not only identify vulnerabilities but also ensure compliance with established policies and regulations.
- Schedule Audits: Conduct safety assessments at least annually, or more frequently if significant changes occur within the institution’s IT framework. This proactive approach helps uncover potential weaknesses before they can be exploited.
- Evaluate Protection Controls: Assess the effectiveness of existing protective measures, including firewalls, antivirus software, and access controls. Regular updates are crucial to ensure these defenses operate as intended.
- Review Incident Response Plans: Evaluate the school’s incident response plans to confirm their effectiveness and relevance. Conduct tabletop exercises to simulate responses to potential safety incidents, ensuring preparedness.
- Document Findings: Maintain comprehensive records of audit findings and the actions taken to address identified vulnerabilities. This documentation is vital for compliance and future audits, providing a clear trail of accountability.
- Continuous Improvement: Utilize audit results to drive continuous improvement efforts. Modify protective policies and practices based on findings to enhance the overall safety posture of the institution.
By implementing regular audits and updates, schools can ensure their information security planning remains effective and responsive to evolving cyber threats.
Conclusion
Implementing effective information security planning in schools is essential for protecting sensitive data and fostering a safe educational environment. By focusing on comprehensive risk assessments, tailored security policies, ongoing training, and regular audits, educational institutions can significantly enhance their cybersecurity posture and mitigate potential threats.
The outlined best practices are crucial for establishing a robust information security framework. Conducting thorough risk assessments enables schools to identify vulnerabilities and prioritize risks. Developing customized policies ensures that data protection measures are relevant and effective. Continuous training for staff and students promotes awareness of cybersecurity threats, while regular audits help maintain compliance and adapt to evolving challenges.
Ultimately, the responsibility for safeguarding sensitive information lies with the entire school community. By embracing these best practices, educational institutions can protect their data and build trust among students, parents, and staff. It is imperative for schools to take proactive steps in information security planning, as the safety and integrity of educational environments depend on the collective commitment to cybersecurity.
Frequently Asked Questions
What is the purpose of conducting comprehensive risk assessments in educational institutions?
The purpose is to effectively safeguard sensitive information by identifying potential threats, evaluating vulnerabilities, and assessing the impact of various risks on the institution.
Who should be involved in the risk assessment process?
A risk assessment team should be assembled, including IT staff, administrators, and educators, to ensure a holistic approach.
What is the first step in risk management for educational institutions?
The first step is to catalog all digital assets, including student records, financial data, and communication systems, to understand what needs protection.
How should potential threats be evaluated?
Potential threats such as cyber-attacks, data breaches, and natural disasters should be analyzed, utilizing resources like the NCSC’s guidelines on cyber protection in educational institutions.
What should schools do to assess vulnerabilities?
Schools should identify weaknesses in current protective measures, such as outdated software or insufficient access controls, and regularly update systems while employing tools like vulnerability scanners.
How can risks be prioritized in the assessment process?
After identifying threats and vulnerabilities, risks should be prioritized based on their potential impact and likelihood to guide resource allocation and investment in safety measures.
Why is it important to document the findings of the risk assessment?
Documenting findings is important to maintain comprehensive records that inform future protection strategies and compliance requirements.
How often should educational institutions conduct risk assessments?
Schools should conduct risk assessments at least once a year to adapt to evolving risks and ensure that their protective measures remain effective.
List of Sources
- Develop Tailored Information Security Policies
- Schools Implementing Robust Data Protection Measures | Case Study (https://cpdonline.co.uk/knowledge-base/safeguarding/schools-implementing-robust-data-protection-measures)
- Implement Ongoing Training and Awareness Programs
- Schools show improved cyber training rates but recovery times slow (https://gov.uk/government/news/schools-show-improved-cyber-training-rates-but-recovery-times-slow)
- The Top 20 Expert Quotes On Cyber Risk and Security (https://surtech.co.za/20-expert-quotes-on-cyber-risk-and-security)
- 38 Cybersecurity Awareness Month Quotes from Industry Experts in 2023 (https://solutionsreview.com/security-information-event-management/cybersecurity-awareness-month-quotes-from-industry-experts)
- 29 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- Conduct Regular Security Audits and Updates
- Schools Implementing Robust Data Protection Measures | Case Study (https://cpdonline.co.uk/knowledge-base/safeguarding/schools-implementing-robust-data-protection-measures)
- Why Educational Institutions Need Secure IT Infrastructure in 2026 (https://3citsolutions.com/why-educational-institutions-need-secure-it-infrastructure-in-2026)

